Tech Specs
Blockchain Entities
Technical specifications and blockchain architecture details for Phala Network.
Overview
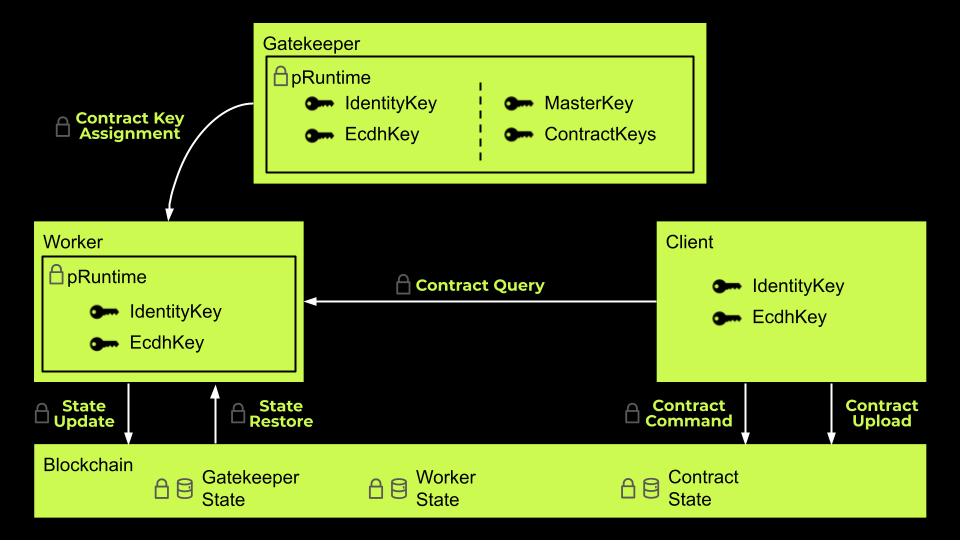
The last chapter covered Phala’s architecture, whereas this page will touch on Phala’s entities and the types of nodes that make Phala Network. In Phala Network, there are three kinds of entities:- Client, which operates on normal devices without any special hardware requirements;
- Worker, which operates on Secure Enclave and serves as the computation nodes for confidential smart contracts;
- Gatekeeper, which operates on Secure Enclave and serves as the authorities and key managers;
Entity Key Initialization
In Phala, the communication between any entity should be encrypted, so each entity generates the following entity key pairs with a pseudorandom number generator during initialization:IdentityKey- an
sr25519key pair to uniquely identify an entity;
- an
EcdhKey- an
sr25519key pair for secure communication;
- an
pRuntime Initialization
During initialization,pRuntime automatically generates the entity key pairs above with a random number generator. The generated key pairs are managed in pRuntime in the Secure Enclave, which means the workers and gatekeepers can only use it with the limited APIs exported by pRuntime, and can never gain the plaintext key pairs to read the encrypted data out of the Secure Enclave.
The generated key pairs can be locally encrypted and cached on the disk with Sealing and decrypted and loaded when restarting. This applies to both gatekeepers and workers.
Secure Communication Channels
TheEcdhKey public key in the pRuntime of a worker or gatekeeper is publicly available. Therefore an ECDH key agreement protocol can be applied to establish a secure communication channel between a worker (or a gatekeeper) and any other entity non-interactively.
A channel between two entities, A and B is denoted as , where and are the public keys of their ECDH key pairs correspondingly. A shared secret can be derived from one’s ECDH private key and the counterpart’s public key via the Diffie Hellman algorithm. Then the final communication key CommKey(A, B) can be calculated via a one-way function. Finally, CommKey(A, B) is used to encrypt the messages between the two entities.
In Khala, theThe public keys of the entities are registered on-chain. So we can build on-chain or off-chain communication channels:EcdhKeyis ansr25519key pair. We can adopt the child key derivation (CKD) functions from Bitcoin BIP32 to deriveCommKey(A, B)from the key agreed by ECDH. The messages are end-to-end encrypted withaes-gcm-256.
- On-chain Communication
- Both
AandBknow each other’s public keys from the blockchain. They can derivesCommKey(A, B); Aposts a cipher message encrypted byCommKey(A, B)to the blockchain;Breceives it, and decrypts it withCommKey(A, B);
- Both
- Off-chain (
Ais off-chain andBis an on-chain worker) CommunicationAcan learnB’s public key from the blockchain and deriveCommKey(A, B);Alearns the API endpoint ofBfrom itsWorkerInfoinWorkerStateon chain;Asends a signed cipher message (encrypted byCommKey(A, B)) with its public key toBdirectly;BgetsA’s public key from the message, and derivesCommKey(A, B)to decrypt it;
Client-worker Payload Example
A client communicates with a worker only for contract invocation. An invocation consists of at least the following payloads.nonceis necessary for defending against Double-spend and Replay Attacks.fromshows the identity of the caller, and can be verified withsig.fromwill be further passed to the contract.- Since a worker can run multiple contracts (or even different instances of the same contract),
tois needed to specify the invocation target. inputencodes the invoked function and arguments, it should be serialized according to the ABI of contracts.
Serialization
Unlike the
EcdhKeyRotationIdentityKeywhich shows the identity of a worker or gatekeeper thus should not be changed, we recommend a regular rotation of theEcdhKeyto ensure the security of the communication channels between different entities. In the future,pRuntimewill automatically rotate the managedEcdhKeykey after certain time interval.

